Secure Information Monitoring: Protecting Your Confidential Details
Are you concerned about the safety of your personal details? In this write-up, we will discuss the value of safe and secure data administration and provide you with finest practices to safeguard your beneficial information. You'll learn regarding typical dangers to your information and just how to carry out efficient data encryption. We'll additionally explore the value of access controls and also customer authorizations, along with the need for information backup and also calamity recovery measures. Keep checking out to guarantee the safety of your delicate data.
The Value of Secure Data Management
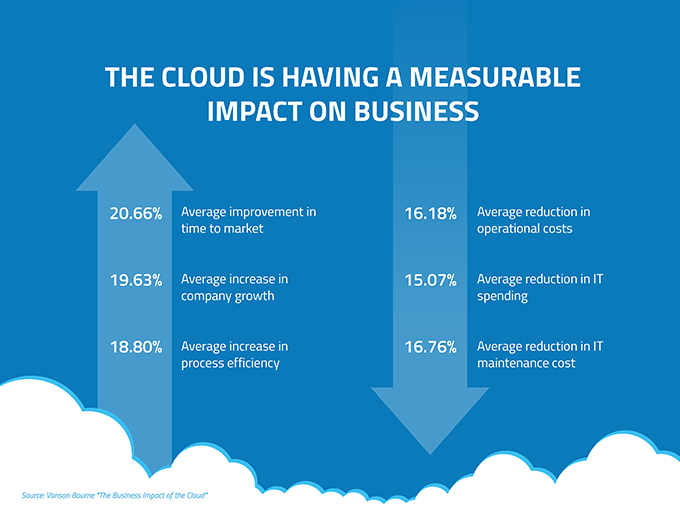
The value of secure data administration can not be overemphasized in today's electronic age. As an individual, you depend on innovation for different facets of your life, whether it's electronic banking, social media sites, or keeping personal information. With the raising frequency of cyber risks, it is crucial to focus on the safety of your data.
When you manage your data firmly, you make certain that only licensed individuals have access to your confidential info. This secures you from identification burglary, economic fraudulence, and other harmful activities. By executing strong passwords, encryption, and regular back-ups, you significantly decrease the danger of your information falling right into the incorrect hands
Furthermore, protected information management likewise profits organizations as well as services. As a local business owner, you have an obligation to secure your consumers' delicate information, such as charge card info or individual information. Failing to do so can cause reputational damage, lawful consequences, and financial losses. By prioritizing protected data management practices, you demonstrate your dedication to protecting your consumers' personal privacy as well as building count on within your community.
Typical Threats to Secret Information
Be aware of typical hazards that can endanger your private data. Cyberpunks can obstruct your data when you connect to unsafe networks, potentially exposing your personal and monetary info. By being aware of these typical dangers, you can take proactive steps to protect your confidential data as well as guarantee your online safety and security.

Best Practices for Information Security
See to it you're using special and solid passwords for encrypting your delicate information. When it concerns protecting your secret information, data file encryption is essential. File encryption converts your information right into a secret code, making it unreadable to unapproved individuals. The toughness of your encryption exists in the password you pick.
Stay clear of using usual expressions or conveniently guessable details, such as your name or birthdate. This way, also if one password is compromised, your other accounts remain safe and secure.
Remember to routinely upgrade your passwords to keep a high level of security. Set pointers to change your passwords every few months or whenever there is a data breach. By doing so, you lower the threat of someone acquiring unauthorized access to your secret information.
Implementing Gain Access To Controls and Customer Approvals
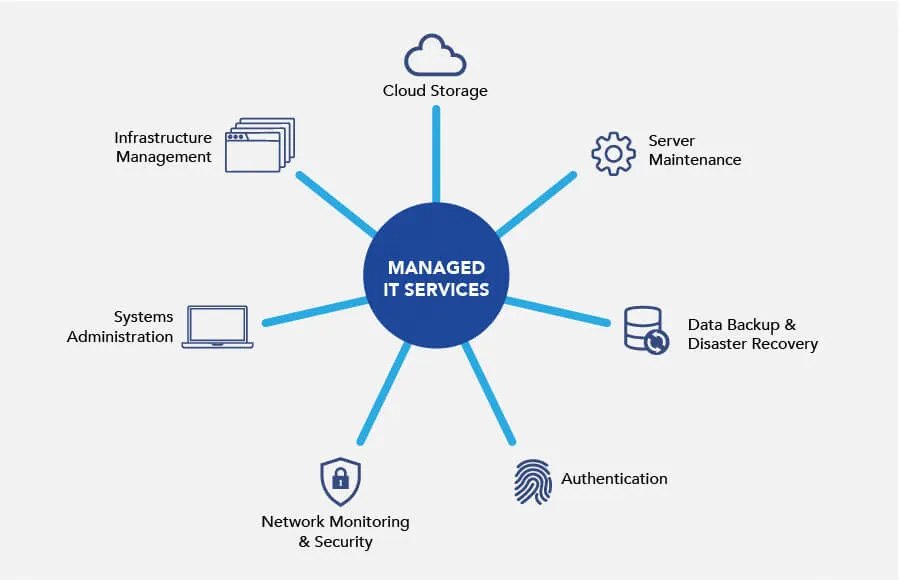
Guarantee that you frequently review as well as readjust gain access to controls and also user permissions to maintain the safety of your delicate data. By applying efficient accessibility controls and customer authorizations, you can dramatically minimize the risk of unapproved access to your secret information.
Beginning by regularly examining the accessibility manages in area. This includes evaluating who has accessibility to what information as well as ensuring that it straightens with their roles as well as obligations within the company. As employees join or leave the firm, it is vital to immediately update their access benefits to stop any type of potential violations.
In addition to evaluating access controls, it is necessary to readjust individual approvals as needed. User consents identify what actions a person can carry out on the information they have accessibility to. By approving the suitable degree of approvals per user, you can limit their abilities and also reduce the danger of information abuse or unexpected removal.
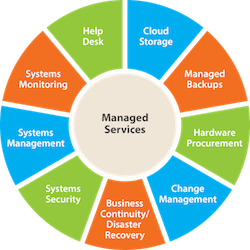
Routinely readjusting and examining gain access to controls and customer authorizations is a recurring procedure - Managed IT Services. As your company grows and advances, it is essential to stay on par with changes as well as make sure that your data stays secure. By doing so, you can safeguard your sensitive information from unapproved gain access to and also keep the honesty and also privacy of your data
Data Back-up as well as Catastrophe Healing Actions
Routinely supporting your data is vital for catastrophe healing in situation of unpredicted occasions. It is essential to have a backup plan in area to safeguard your useful information and make certain service continuity. By routinely backing up your data, you can minimize the influence of data loss due to hardware failures, all-natural disasters, or cyberattacks.
Having a trustworthy back-up system enables you to recover your information swiftly as well as effectively, decreasing downtime and preventing possible economic losses. Whether you select to back up your information on external hard disks, cloud storage, or a mix of both, it is vital to set up normal backups to guarantee that your latest details is protected.
In enhancement image source to regular backups, it is equally Full Article vital to check your back-up systems as well as refines routinely. When required, this makes certain that your backups are working effectively as well as that you can efficiently recover your data. By testing your backup systems, you can determine any type of possible problems or voids in your calamity healing plan as well as address them proactively.
Final thought
To conclude, handling and protecting your secret information is vital in today's digital landscape. Video Conferencing. By implementing protected information management techniques such as security, accessibility controls, and data backup actions, you can safeguard your useful data from usual risks. Bear in mind to frequently upgrade your safety methods to stay one action in advance of possible violations. By focusing on the security of your secret information, you can make certain the trust fund and self-confidence of your stakeholders and also clients. Don't wait any type of longer, take activity now to safeguard your information!
In this article, we will certainly discuss the importance of protected information administration as well as supply you with finest techniques to secure your important data. When you handle your information securely, you make sure that only authorized people have accessibility to your Click This Link personal details. When it comes to protecting your confidential details, information file encryption is crucial. By frequently backing up your data, you can reduce the effect of data loss due to equipment failures, natural disasters, or cyberattacks.
By executing protected information monitoring practices such as file encryption, gain access to controls, and information backup steps, you can protect your useful data from usual hazards.